Browser extensions are designed to improve functionality and enhance your browsing experience. From ad blockers to emoji keyboards, these tools provide convenience and customization. However, cybercriminals have increasingly exploited these trusted tools to inject malicious code, steal data, and manipulate web content.
How Cybercriminals Exploit Browser Extensions
A recent security report uncovered a breach that affected over 3.2 million users, where legitimate browser extensions were compromised through a supply chain attack. Threat actors infiltrated trusted extensions, injecting malicious updates that secretly collected data, manipulated web content, and delivered ads — all without users noticing.
While some malicious extensions are intentionally designed to steal information, this attack exploited legitimate extensions that had originally served a useful purpose. By embedding harmful scripts within routine updates, attackers leveraged the extensive permissions these extensions were granted, making it difficult for users to detect the threat.
Extensions Identified in the Breach
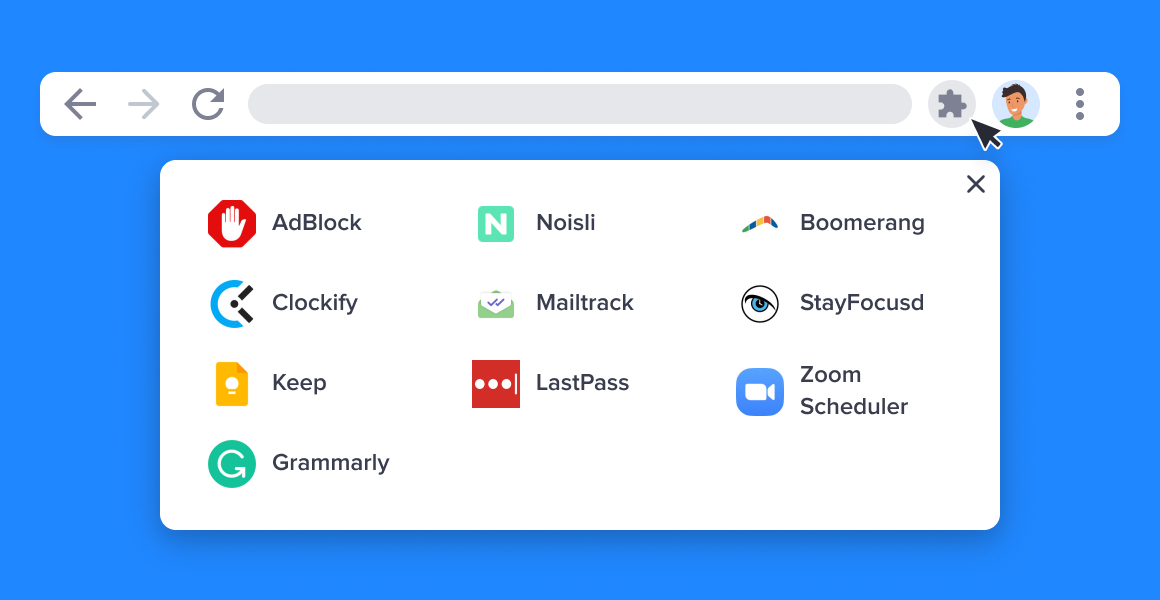
Some commonly used extensions that were compromised include:
- Blipshot (full-page screenshot tool)
- WAToolkit (WhatsApp Web utility)
- Super Dark Mode (dark theme for websites)
- Page Refresh (automated page refresh tool)
- Various ad blockers such as Mike Adblock für Chrome, Adblock for Chrome, and Adblock for You
If you recognize any of these extensions in your browser, it’s essential to review their permissions and consider removing them until their security is confirmed.
Why Were These Extensions Vulnerable?
The attackers exploited the automatic update process of trusted browser extension stores like the Chrome Web Store. They bypassed standard security protocols such as Content Security Policy (CSP) protections, enabling them to alter web content and communicate with remote servers to receive new instructions. Evidence suggests this attack campaign had been active since mid-2024.
How to Verify Trusted Extensions
To reduce the risk of compromised extensions, follow these steps:
- Verify the Developer: Always check the publisher's identity in official stores like the Chrome Web Store or Firefox Add-ons. Established brands such as Google, Microsoft, or Norton are safer bets.
- Check Reviews and Downloads: Malicious extensions often have fewer reviews, lower ratings, or vague feedback. Stick to extensions with a substantial user base and positive reviews.
- Avoid Third-Party Websites: Only download extensions from official sources to minimize exposure to fake or harmful versions.
- Monitor for Unusual Behavior: Extensions that request excessive permissions, slow down browsing, or inject unexpected ads could indicate compromise. Remove suspicious extensions immediately.
Six Steps to Protect Your Personal Data
- Update Your Browser and Extensions Regularly: Outdated software is a prime target for attackers. Enabling automatic updates ensures you receive security patches promptly.
- Install Extensions Only from Trusted Sources: Avoid downloading extensions from unfamiliar websites or links.
- Use Strong Antivirus Software: Reliable antivirus tools can detect and block malicious scripts embedded in browser extensions.
- Review Extension Permissions: Periodically audit the permissions granted to each extension. Revoke unnecessary access whenever possible.
- Limit the Number of Extensions Installed: The fewer extensions you use, the smaller your attack surface.
- Stay Alert to Suspicious Activity: If your browser behaves oddly — such as frequent crashes, slowdowns, or unexpected pop-ups — investigate and remove potentially harmful extensions.
Final Thoughts
While browser extensions can significantly improve productivity and browsing experience, they also present security risks if not managed carefully. Regularly audit your installed extensions, limit permissions, and stay vigilant against suspicious behavior to safeguard your personal information online. If you are worried about any particular extensions or realize you have one of the compromised extensions listed above, you can contact Ascend Technology Group.